TOP STORIES
Thoras.ai Secures $1.5M to Boost Enterprise Cloud Optimization and Resilience
Thoras.ai announced the successful closure of a pre-seed funding round of $1.5 million.
Read MoreCheck Point and NVIDIA Secure the Future for AI in the Cloud
The new Check Point AI Cloud Protect solution integrates with NVIDIA's data processing units, or DPUs, to defend against …
Read MoreSecurity Concerns Hinder Adoption of GenAI in Major Companies
PagerDuty announced the latest findings from its recent study which sheds light on the sentiments of technology executives at America'…
Read MoreAvaya Introduces New Communication and Collaboration Suite
The Avaya Communication and Collaboration Suite is a platform designed to streamline communication and collaboration experiences for customers.
Read MoreThe CX Hot Six for Telecoms Learning Center
 The CX Hot Six for Telecoms
The CX Hot Six for Telecoms
A guide to customer experience technology that delivers on business KPIs
LATEST FROM COMMUNITIES
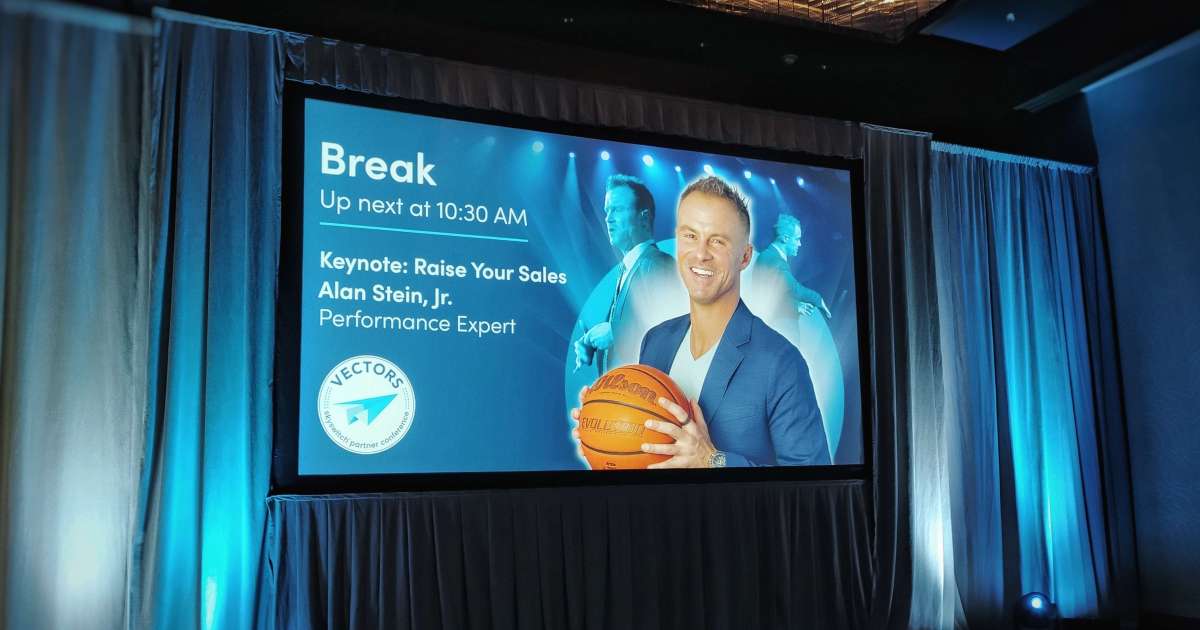
A Winner's Mindset: Alan Stein Jr. Helps Businesses Build Winning Teams
At SkySwitch Vectors 2024 in downtown Nashville, Tennessee, last week, the keynote speaker was Alan Stein Jr. He stylishly pr…
Read MoreAtomicwork and Cohere Partner on AI-Powered Workplace
Atomicwork launched its innovative digital workplace experience solution, co-developed with Cohere.
Read MoreBusinesses Face Security Woes in the Age of AI
Organizations may struggle to keep pace with evolving security landscapes, particularly in the face of AI advancements and th…
Read MoreHumane AI Pin gets off to a rough start
San Francisco-based company Humane Inc. launched the AI Pin in November last year. Now available nationwide for $699, this we…
Read More8 Clinical Trials That Will Shape Medicine in 2024
One of the exciting things about modern medicine is that it is making increasingly rapid advancements in a number of key area…
Read MoreNavigating the Dark: A Buyer's Guide to Choosing the Best Night Vision Monocular
The cloak of night, with its mysteries and allure, beckons adventurers, wildlife enthusiasts, and security-conscious individu…
Read MoreHow Monochrome LCD Screens Help Shape the Medical Industry Today
As regular users of different types of technology, we witness great inventions coming out almost each day and it's more than …
Read MoreHow to Pack First-Aid Kit for Unexpected Health Emergencies: Alaska Winter Edition
Vacations are super important for our mental and physical health. Getting away from the city is all one needs. It's the best …
Read MorePowering Adaptability in IoT: Telit Cinterion Reveals its First High-Precision GNSS Module
Telit Cinterion announced the launch of its SE868K5-RTK module, a high-precision Global Navigation Satellite System (GNSS) re…
Read MoreNext-Generation Tactics for Boosting Security Across Your Trucking Fleet
In an era where technology is evolving at an unprecedented pace, the transportation industry is no exception. With the rise o…
Read More